The public role
2May 23, 2018 by Kenneth Fisher
A common misunderstanding is that the CONNECT permission lets you do more than just connect to a database. It doesn’t. Connection only. So how come there are some things that everyone can do once they are connected to a database? Well, it’s the public role. Everyone is a member and that can’t be changed. In fact, you can’t even disable it. Oh, and I should point out that every database has one.
So what does that mean? If you have a table that you want everyone to have read access to you could grant the permission in public.
-- Create test login. CREATE LOGIN Public_Only WITH PASSWORD = 'Public_Only', CHECK_POLICY = OFF; USE Test; -- Create a test table and grant read access to the public role. CREATE TABLE Public_Read (Col1 INT); INSERT INTO Public_Read VALUES (1), (2), (3); GRANT SELECT ON Public_Read TO public; -- Create test user. CREATE USER Public_Only FROM LOGIN Public_Only; -- Confirm that the user only has CONNECT permissions to the -- database Test. EXEC sp_DBPermissions 'Test','Public_Only', @Output = 'Report';
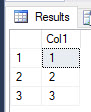
-- Login as Public_Only user USE Test; SELECT * FROM Public_Read;
And there you go. A user with only connect access can read from the table. You can, of course, do the exact opposite and DENY read to a table. That would make it so that only the database owner (dbo, not members of the db_owner role), sa, and members of the sysadmin role would be able to read from the table.
This type of technique can be particularly handy if you are building a logging table of some type that you want everyone to have write access regardless of their other permissions. You do want to be careful though because, again, anything you do affects everyone
Category: Microsoft SQL Server, Security, SQLServerPedia Syndication | Tags: database permissions, microsoft sql server, roles, security
2 thoughts on “The public role”
Leave a reply to Be our guest, be our guest, put our database to the test. | SQL Studies Cancel reply
This site uses Akismet to reduce spam. Learn how your comment data is processed.







[…] Kenneth Fisher explains the public role in SQL Server: […]
[…] I think of the public role I often think of the guest database principal (user) at the same time. They aren’t really the […]